A major vulnerability in the Companies House website gave unauthorised access to the private dashboard of any of the five million registered companies for five months. It exposed directors’ home addresses and email addresses, and enabled attackers to change company and director details – and even file accounts.
This article sets out what we know, what we don’t, and what businesses should be doing to protect themselves. Updated 17 March 2026 with Companies House letter.
What is now confirmed:
- Unauthorised access to any company’s dashboard
- Vulnerability existed since October 2025
- Bad actors could access non-public personal data
- Bad actors could file accounts and company/director changes
What remains unconfirmed:
- Whether it was exploited by criminals
- Whether Companies House can identify affected companies
The vulnerability
It’s incredibly simple, and involves just pressing the “back” key at a particular time.
The vulnerability was discovered on Thursday 12 March by John Hewitt at Ghost Mail, a corporate services provider. He tried to contact Companies House immediately, but didn’t get a response – so he contacted us. This is a video of the Zoom call when John first demonstrated the vulnerability to me (edited only to redact personal information):
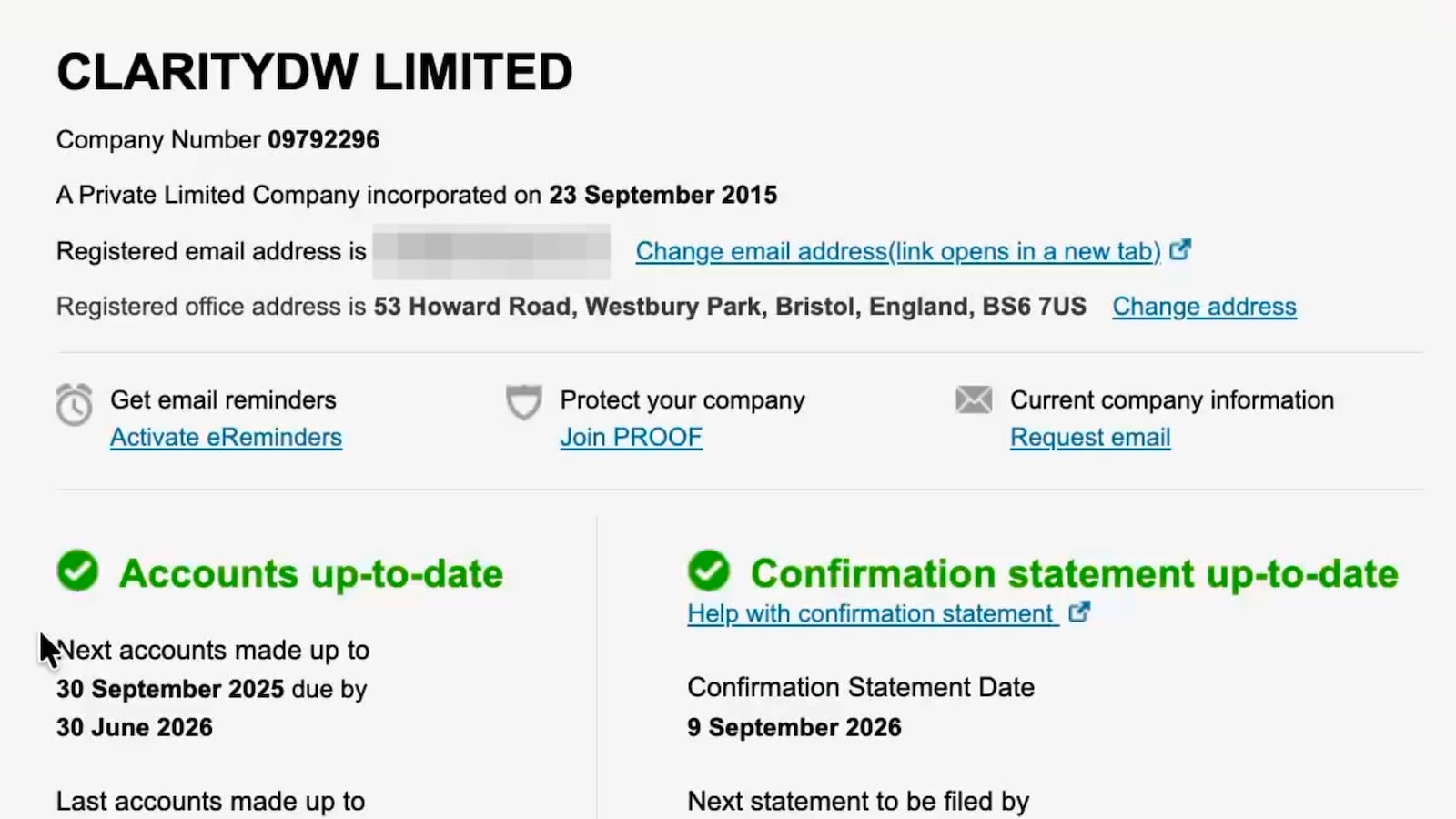
John used the vulnerability to view the private Companies House dashboard of ClarityDW Ltd, a digital communications consultancy owned by Jonathan Phillips. Jonathan kindly gave us permission to do this.1
John then used it to view the dashboard of a company I own, and to modify my own registered address. That appeared to work, as it generated a confirmation number. As you will hear, I was incredulous at what John showed me.
I then spoke to computer security specialists. To rule out the possibility that it was something specific to John’s computer, network or account, I tested the vulnerability myself (again using Jonathan’s company as the target):
This shows the exploit revealing private information that’s not published by Companies House, such as personal email addresses and full dates of birth (and you can see that in the video, with Jonathan’s personal information masked).
These are precisely the kinds of data used for fraud: impersonation, phishing, identity checks, and social engineering – particularly targeting directors of small companies (as large companies generally have systems that mean one person alone cannot authorise payments).
I therefore alerted Companies House immediately. They responded swiftly by shutting down the e-filing system, and only after that did we (and the FT) publish this story.
How the exploit works
When John first contacted me, I assumed this was a highly technical exploit or “hack”. It was nothing of the sort.
All that was required was to log in to Companies House using your own details and access your own company’s dashboard. Then opt to “file for another company” and enter the company number for any one of the five million companies registered with Companies House. At that point you’d be asked for an authentication code, which of course you don’t have. No problem. Press the “back” key a few times to return to your dashboard. Except – it isn’t your dashboard. It’s the other company’s dashboard.
Anybody wishing to take advantage of the exploit could, for £100, incorporate their own company and obtain dashboard access (and there are various ways this could be done without leaving any trace back to those responsible).
Does the exploit enable modification of company data?
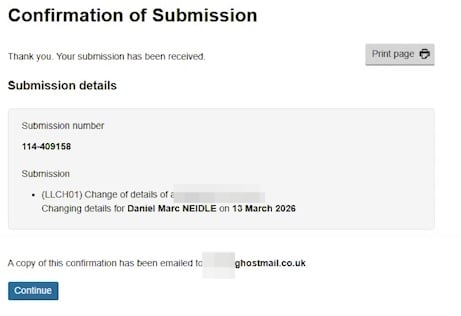
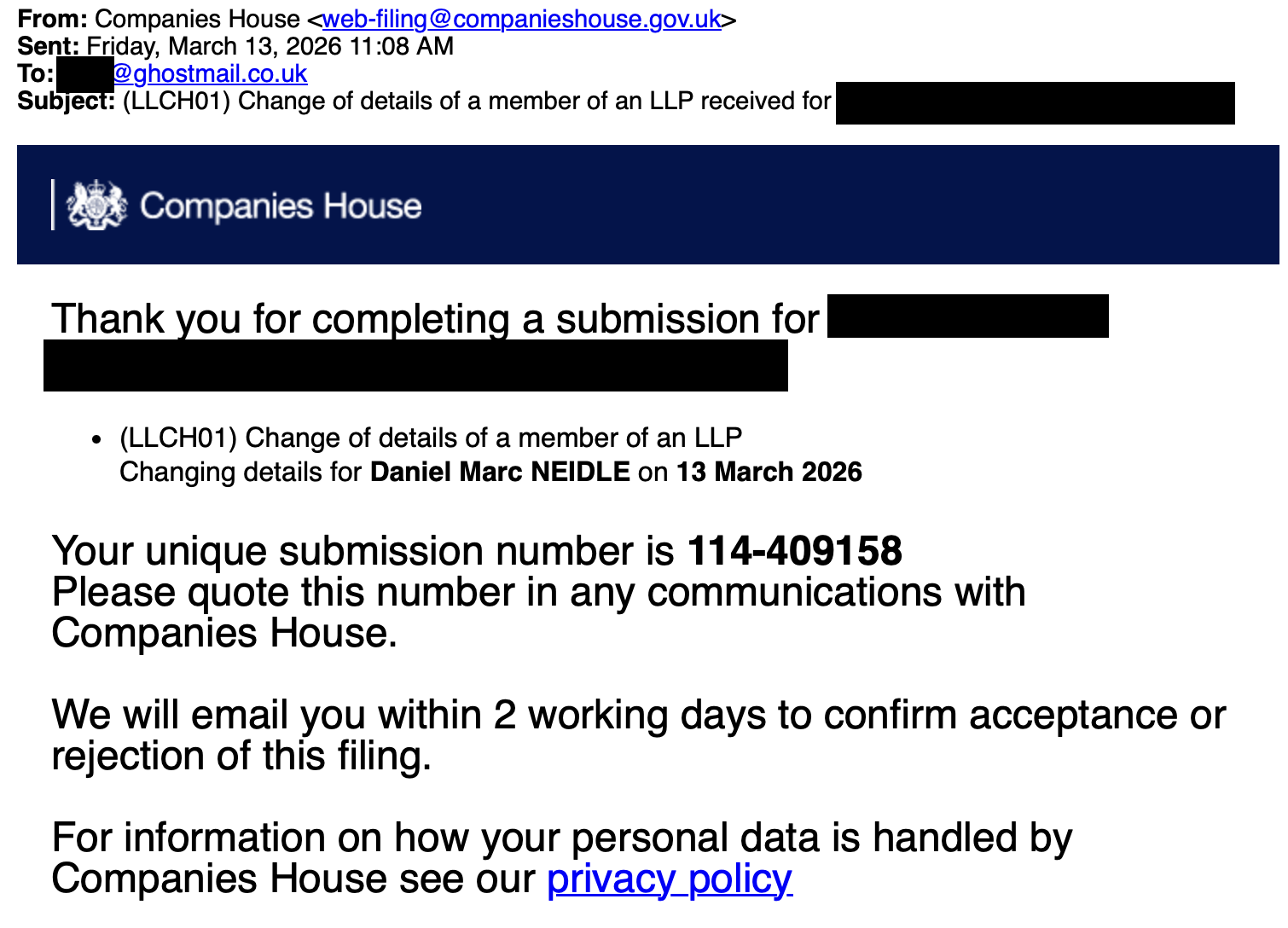
In the first video, you can see John changing my own registered address for a company (this was with my permission, and it needed changing anyway). The change appeared to go through, and we saw this confirmation:
There are two notable things here. First, we received a submission number. The technical experts we spoke to said that, whilst it was possible the edit was not really going through, the fact we saw a submission number suggested that it was. Second, the copy of the confirmation was emailed to John, and not to me (even though it was my company):
This is extremely dangerous, because it means that any company that falls victim to this exploit would not receive a warning email.2
We concluded from this that any filings could be made for any company, including changing registered office, director names/addresses, and filing accounts.
Has the vulnerability been exploited?
We don’t know. Five months is a long time for a vulnerability this serious to remain live. Research suggests that newly discovered vulnerabilities are, on average, exploited within 15 days.
The security experts we spoke to thought that, if the exploit had been live for longer than a few days, then there was a high chance that bad actors had discovered it.3 It could then have been sold to an organised group (on Telegram or the “dark web”).
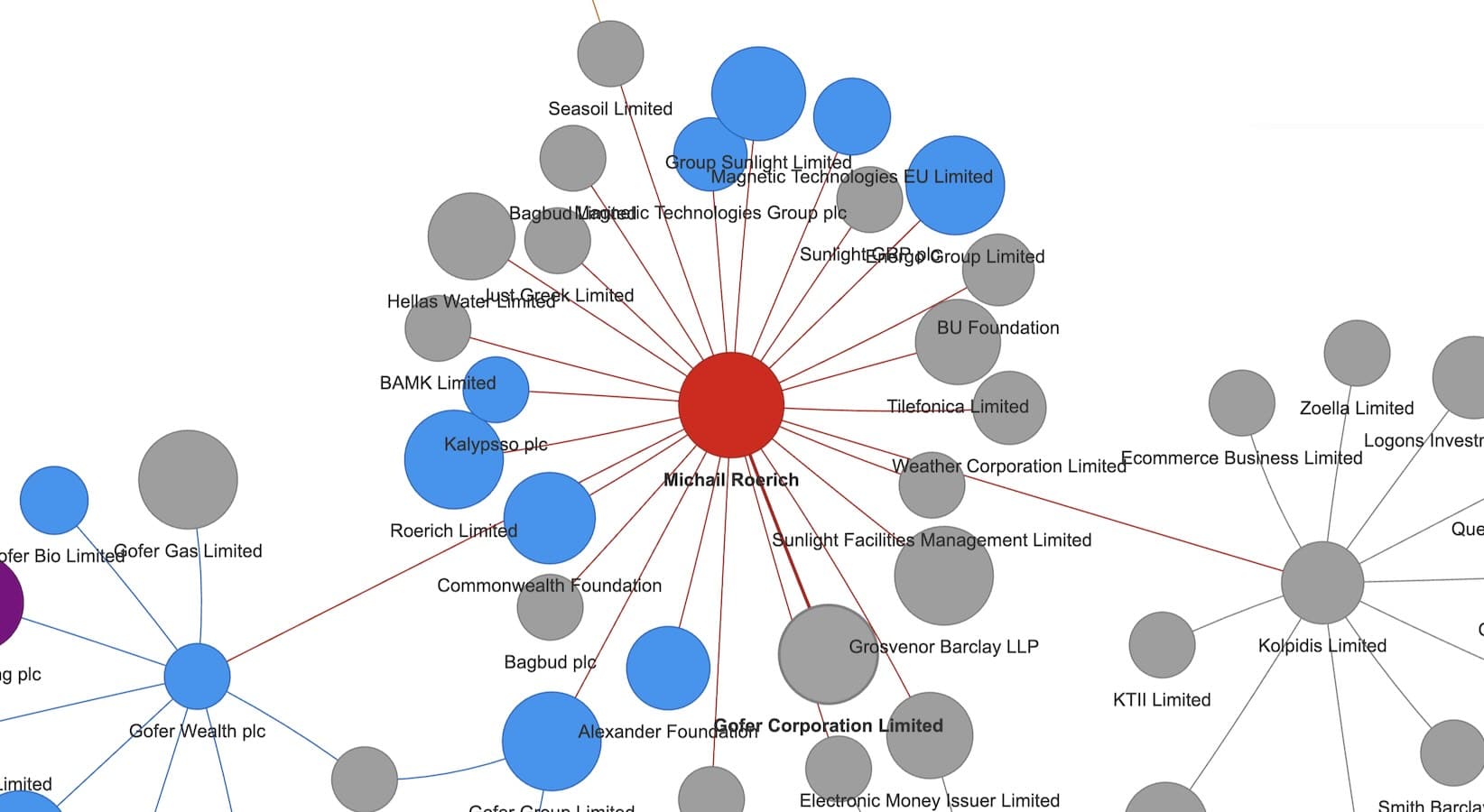
It would be technically straightforward to scrape the hidden personal details of the directors of all five million companies, but sophisticated bad actors would expect that to trigger alerts at Companies House. A sophisticated criminal group would probably not use this exploit in the most obvious way. They would use it carefully, selectively, and for profit.
The experts we spoke to identified these as more likely uses of the exploit:
- Use open source research to identify individuals vulnerable to identity fraud – and this would be more likely to be directors of small companies than billionaires. Then use the exploit to find their personal data – but limit this to hundreds of companies rather than millions.
- If the exploit really does enable modification, then identify small companies that could plausibly borrow large amounts from banks, and change their details so that the criminals can open bank accounts and borrow in the name of those companies. This would be carried out on a small scale – say 20 companies each week borrowing £50,000 each. It would take some time for banks and/or authorities to realise that this was more than “conventional” fraud by e.g. forging signatures and intercepting post.
Companies House’s response
We told Companies House of the vulnerability as soon as we became aware of it; soon afterwards, the web filing system shut down, presenting this error message, and this on the “service availability” page:
On Monday 16 March, Companies House published a full statement revealing that the vulnerability had been live for five months.
And on 17 March, Companies House sent an email to every company in the UK:
I am a little concerned that this is minimising what happened:
- Saying the vulnerability “could only have been exploited by a logged-in user performing a specific set of actions” downplays the ease of bad actors gaining a Companies House login (very easy: just pay £100 to incorporate a company).
- The “specific set of actions” sounds like it was something very obscure, when actually it was just pressing the “back” key four times. Given there are five million companies, and the vulnerability was present for five months, it would be surprising if it wasn’t discovered by accident on multiple occasions. The key question is whether it was ignored or exploited.
- “It is not a cyber-attack” is true but is failing to disclose the actual risk – that the vulnerability could have been used to modify company data and then engineer a fraud on that company or its commercial counterparties/lenders.
- It leaves open the question of whether Companies House actually can ascertain if the vulnerability was used to access or modify data. The security experts we spoke to thought that, if Companies House had standard audit logging in place, it should be able to see which logged-in accounts accessed unrelated companies’ dashboards, when that happened, and whether they then attempted filings or changes. That ought to make at least some retrospective investigation possible.
What happens next
There are obvious security and GDPR implications of revealing directors’ home and email addresses for millions of companies. All the more so if nobody knows which companies were impacted by the vulnerability.
Companies House has obligations under UK GDPR:
- to notify the Information Commissioner within 72 hours (it appears this has been done), and
- because this is a “high risk breach“, to notify all those affected “without undue delay”. The general alert (as above) partly satisfies that, but if Companies House becomes aware that any company’s specific data was accessed or modified then they would be required to notify that company.
We expect the Information Commissioner’s Office would take this very seriously, although its usual policy is not to fine public authorities.
What should businesses be doing?
At the present time we have no idea if the exploit was used by bad actors (or indeed just pranksters).
It would seem very sensible for all companies to check their Companies House data and make sure it is as they expect.
Thanks most of all to John Hewitt at Ghost Mail. I hope he receives formal thanks from Companies House.
Thanks to Jonathan Phillips for helping verify the vulnerability, and allowing his own company to be used as a guinea pig.
Thanks to P, T and K for their computer security expertise, and B for Computer Misuse Act advice.
Footnotes
Any “penetration testing” of Companies House has to be conducted very carefully because of the potential to commit a criminal offence, under either the Companies Act or the Computer Misuse Act. Neither has a public interest defence. In our case, access was authorised (by me and Jon) so no offence is committed under the Computer Misuse Act, and whilst John did modify my company data, the modification resulted in accurate data being submitted to Companies House. ↩︎
We couldn’t immediately see if our test change was effective, because it normally takes around 24 hours for changes to be reflected in the dashboard – and the dashboard was shut down almost immediately afterwards. As of Monday 16 March, the dashboard is back up, and this change has not gone through. However that may be because the specific change we made was blocked by Companies House; their email (below) confirms that changes could be made. ↩︎
The “easy” nature of the exploit paradoxically means that the usual automated vulnerability scanners would probably not detect it; however the number of bad actors routinely using Companies House for nefarious purposes means that they could just have discovered it the same way John did. ↩︎





Leave a Reply